Category: Windows Server
-
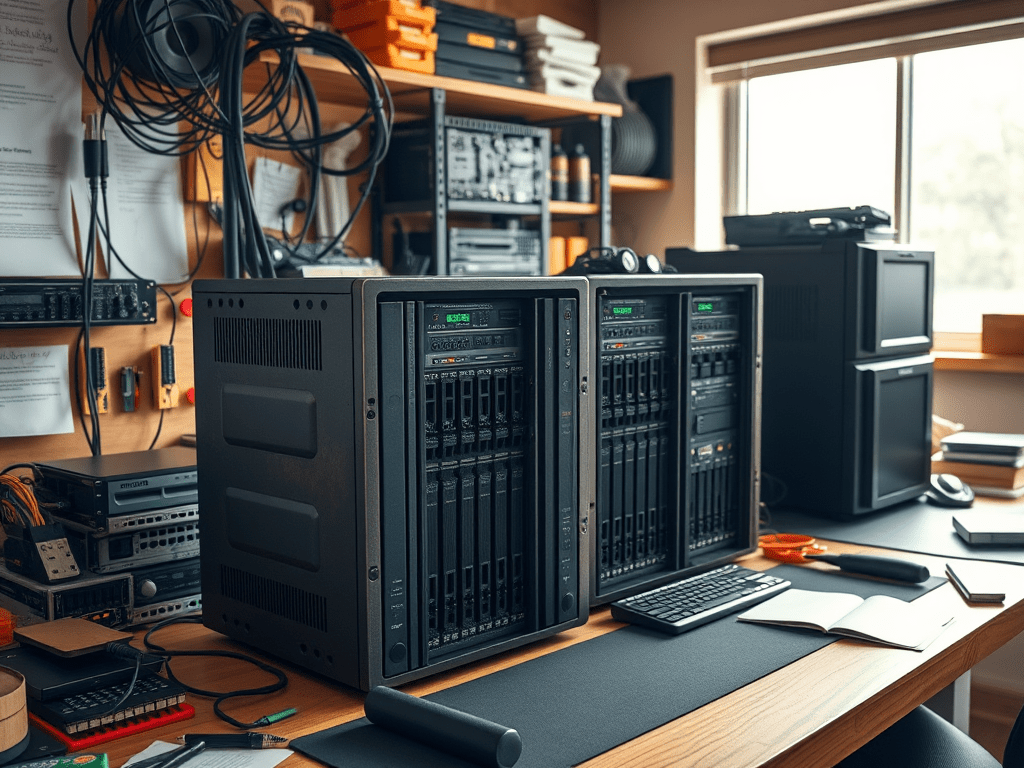
The Lab at Home
There was a time when this blog was all the rage. I have not maintained it the way that I wish I could, but the truth is that life gets in the way. These last few years I have spent more time teaching, and until my life settles down that is not likely to change.…
-
Has it been that long?
The first public presentation that I delivered to a Microsoft community audience was the launch of Windows Server 2003 R2. As a user group leader at the time, I was sent a copy of the product, along with a lot of materials to help me to deliver the presentation in the MPR room at Microsoft’s…
-
The Secrets of The French…
The first class that I took on Microsoft Windows was with a very nice French-Canadian instructor whose name I think was Denis. He told an interesting story that I wish I had retained the details of. He told us that following The Great War (WW1), the government of France decided that codes and secrets and…
-
Errors Unknown and Unknowable
Every so often I encounter a problem that needs to be escalated. This one had a lot of us scratching our heads for a couple of weeks. It is a French server, but in simple terms: When trying to run the Hybrid Configuration Wizard to connect the Exchange Server to Exchange Online, we ran into…
-
Where’s my RSAT?
A close friend and former colleague recently gave me the nickname “Mr. No GUI.” Why? I am big believer in Windows Server Core. I do not believe there should be a GUI on a Windows Server unless it is being used as a desktop. That does not mean that we all have to become command…
-
RSAT Tools
**DISCLOSURE: While I am contracted to Microsoft Corporation, I am not an employee. The articles that I write are not meant to represent the company, nor are they meant to represent me as an employee or spokesman for the company. As has always been the case, all articles on this website represent me and nobody…
-
Domain Controller to the Core
**DISCLOSURE: While I am contracted to Microsoft Corporation, I am not an employee. The articles that I write are not meant to represent the company, nor are they meant to represent me as an employee or spokesman for the company. As has always been the case, all articles on this website represent me and nobody…
-
Renaming Your Domain
**DISCLOSURE: While I am contracted to Microsoft Corporation, I am not an employee. The articles that I write are not meant to represent the company, nor are they meant to represent me as an employee or spokesman for the company. As has always been the case, all articles on this website represent me and nobody…
-
Event Viewer Tasks: Get rid of them!
A little while ago I was demonstrating some of the functionalities of the Windows Event Viewer. It has been around for so many years, and yet there are people who have not used it. One of the functions that I demonstrated was attaching a task to an event… so when a particular event happens, a…
-
Domain Controller Ports
Recently I was asked by a client to produce a list of firewall ports that are used by Active Directory Domain Services (AD DS), specifically those for domain controllers. This is what I came up with: TCP and UDP 389 Directory, Replication, User and Computer Authentication, Group Policy, Trusts LDAP TCP 636 Directory, Replication, User…
-
Server 2016 Versions & Builds
When Microsoft introduced the Operating System as a Service with Windows 10, a lot of people got started getting confused because of the different version numbers and build numbers, all the while Microsoft was telling us it was really the same operating system. Okay, I think we have it clear now… three years later. So…
-
Delegating Control in Active Directory
I have been saying for years that a good IT department in a secure, well-managed infrastructure will give their end users the tools they need to do their job… and nothing more. If that is true for end users, shouldn’t it also be true for the IT department themselves? It is frustrating to see the…
-
Offline Files: Groan!
You’ve configured Folder Redirection in Group Policy, and it works as expected… as long as you are connected to the network. As soon as you disconnect, things stop working. That may be a real inconvenience if you are redirecting your Photos, but if you have redirected your Desktop folder to a network share, there is…
-
KB4103723: DO NOT APPLY!
Hey folks, if you know what is good for you, do not apply this patch yet. KB4103723 protects against a CredSSP vulnerability that has not yet been compromised. However, it will break lots of things in your system, including RDP and Hyper-V connections. Errors will include CredSSP errors when trying to connect via RDP (or…

