-
Not a Security Person…
I was approached about a job recently by a company I have worked with in the past. While speaking with the recruiter he told me that one aspect of the position was Identity and Access Management (IAM). He then told me that the client had specifically told him that “This job is NOT related to…
-
Certified in Cybersecurity
I have been security-minded for most of my adult life. Whether or not I have always lived it is another matter, but I have learned my lessons and have done my best to continually improve. While I have been taking IT certification courses and exams for nearly twenty-five years, it was only in 2022 that…
-
Goodbye to an Era

In the days after the demise of cassette tapes and before MP3s existed there were basically two ways get your music legally: You could listen to the radio of course… but the vast majority of people purchased it on Compact Disc (CDs). Tower Records reigned supreme but there were many other places to purchase them……
-
Security Copilot: WARNING!

I have been a technology blogger since 2002. I could not possibly go back to count, but I would not be surprised if I have written over a thousand articles on or around Microsoft products, technologies, events, and solutions. Whether you have read one or two, or all of them, I can guarantee you that…
-
Domain vs. Entra… or both?
This will be the first of a multi-part series on configuring and managing device Identity and Access Management (IAM) for Microsoft In the year 2000, Windows 2000 Server was released, and with it came a new era of authentication. Microsoft introduced Active Directory to the world, which would later be known as Active Directory Domain…
-
Entra ID Connect: Starting Over
Because I do not always run my demo environments following industry best practices, I occationally find myself in a situation where things might be… horked. That is to say, my on-prem lab (including the Active Directory domain) gets wiped, and I rebuild it from scratch. It is something that I usually enjoy doing, and until…
-
Do The Right Thing…
While I have been using and learning computers since 1979, by my own definition I only became a real IT Professional when I passed my first certification exam in 2003. At that time I was already aware of a lot of people in the business who were… less than reputable. When I went out on…
-
Not Passing and Failing
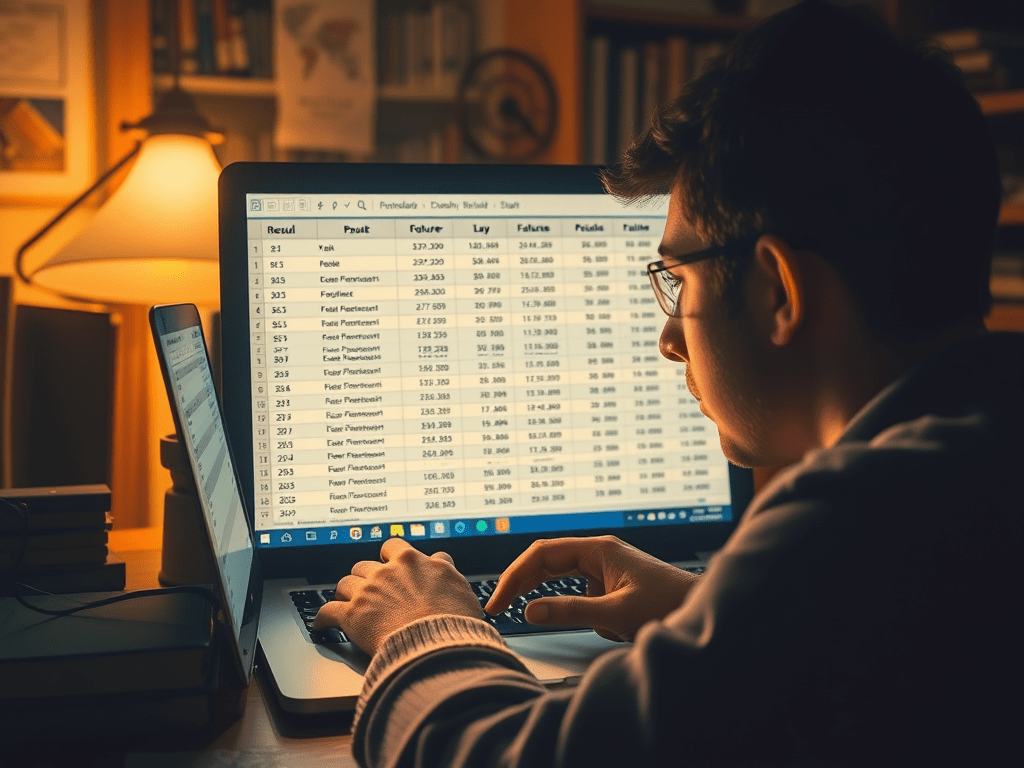
I maintain a spreadsheet that lists every single certification exam that I have sat since my first one in December of 2001. Each line consists of the date, the exam title, the exam code, the result, and the certification that it was applicable to (since many certifications, especially in those early days, required multiple exams…
-
Words Matter
There are some things people say that I look at them and think to myself ‘that was completely insensitive’ or ‘you could have said that in a less hurtful way.’ On the other side of that, I believe that in this day and age people get offended far too easily, and that getting angry because…
-
The Lab at Home
There was a time when this blog was all the rage. I have not maintained it the way that I wish I could, but the truth is that life gets in the way. These last few years I have spent more time teaching, and until my life settles down that is not likely to change.…
-
Online Certification Exams – Are they worth it?
Every class I teach I get questions about certification exams. I do not mean about the value of certifications, although there is that too… and I will revisit that topic in a later article. I mean about the exam experience. When I took my first exams, I had the choice of taking it at a…
-
How Railroads Railed Us
The standard gauge of a railroad in North America and Europe is 4′ 8.5″, or four feet, eight and a half inches. Most people will give that absolutely no thought in their entire life. Of those who do, some will think to themselves, ‘I wonder if that is based on an old unit of measure…
-
Security Baselines in Intune
Okay, if you are a strong believer in cybersecurity, raise your hands. Okay, you can put them all down now. While I know there are people out there who believe that everything should be open to everyone, I doubt they are reading my blog. Next: If you bought/acquired/were gifted/found/inherited your current computer and, before doing…
The World According to Mitch
The day to day ramblings of an IT Professional (and so much more…)
